
When a bank outsources a function to a third party, the regulatory obligation does not transfer with it. The…
A modern AI-powered cyber risk management platform built for cybersecurity & compliance teams. FortifyData brings together attack surface monitoring, third-party risk management, and compliance automation into one unified system designed to reduce cyber risk and improve decision-making.
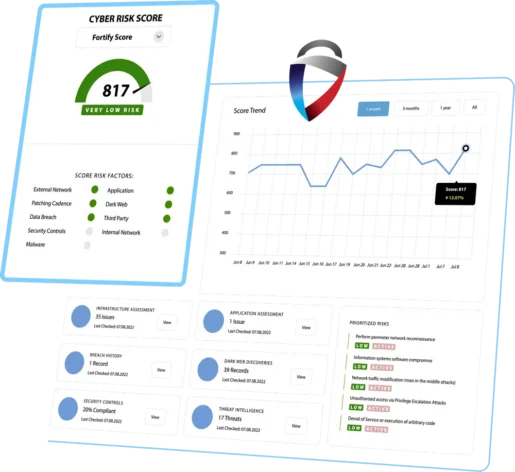
FortifyData delivers cyber risk management software that gives security teams continuous visibility, AI-driven prioritization, and actionable remediation workflows; all in one platform.
Ensure nothing is missed as we continuously map and monitor your entire attack surface
Automated attack surface assessments continuously identify new exposures aligned with your business criticality so your organization can proactively protect against unauthorized intrusions. Focus on what matters most with context based prioritization to expedite remediation.

Tired of reading SOC 2 reports? Save time with AI Audit Dashboard
Upload vendor provided reports and get an AI-powered audit analysis of their report against the principles or controls.
Combining AI-powered report analysis, with agentic vendor management workflows for questionnaires and external assessments of vendors, your TPRM program will take less time and identify the risks you use to spend hours trying to find.

Save time and resources to achieve and maintain compliance.
Automate the tedious tasks of compliance monitoring and reporting, freeing up your team to focus on proactive security while reducing the risk of non-compliance. With risk findings natively assessed and monitored, we seamlessly tie them to applicable framework controls and continuously report on them.

Your operational context drives the likelihood and impact
Our AI-powered risk prioritization understands taht some systems and assets take a priority. Now your team gets a real-time ‘fix list’ with intelligently recommended remediation steps to reduce the most critical risks facing your organization.

The days of $3M GRCs and years to implement are over
Streamline your cybersecurity compliance journey with the advantages our AI-powered platform. Integrate the continuous attack surface, remediation, and third-party risk findings into your compliance and audit program. Save time and resources with a consolidated platform with unified data that seamlessly feeds to your controls.





Gain real-time visibility and stay ahead of threats with intelligent workflows powered by IT risk management software designed for modern cybersecurity teams.
Cyber GRC – Unify governance, risk, and compliance specifically for cybersecurity use cases
Enterprise Risk Management – Centralize risk oversight across departments and functions
Internal Risk Assessments – Automate assessments and evidence collection for stronger internal controls
Identify and mitigate risks across your infrastructure and vendor ecosystem with continuous monitoring.
Attack Surface Management – Eliminate blind spots with complete asset visibility
Vulnerability Management – Detect, prioritize, and remediate vulnerabilities faster
Security Rating – Monitor your own security posture and benchmark against peers
Strengthen your vendor ecosystem with continuous vendor monitoring, AI Auditor of SOC 2 and other vendor reports, AI vendor lifecycle workflows, and real-time attack surface data that goes beyond static questionnaires.
We continue to win business and provide superior value to our clients who preferred the FortifyData approach compared to Security Ratings or Attack Surface Management (ASM) vendors.


FortifyData is a specialized AI-powered cyber risk management platform tailored to cybersecurity and compliance teams. It helps organizations eliminate tool sprawl, improve visibility, and reduce cyber risk—without the complexity of traditional GRC platforms.
FortifyData delivers specialized IT risk management solutions that adapt to the unique risk and compliance needs of every sector. Our unified cyber risk management platform helps organizations across industries strengthen cybersecurity, streamline compliance, and reduce risk.
FortifyData is an AI-powered cyber risk management platform built for security and compliance teams. It consolidates attack surface management, third-party risk management, and compliance automation into one unified platform, eliminating the tool sprawl that forces teams to manage multiple disconnected systems. FortifyData is designed as a force multiplier for under-resourced security teams, delivering continuous visibility, AI-driven prioritization, and defensible risk decisions without adding headcount.
Cyber GRC, governance, risk, and compliance, is the discipline of managing cybersecurity risk in alignment with organizational governance requirements and compliance frameworks. Unlike traditional GRC platforms that were built for broad enterprise risk management, cyber GRC platforms are purpose-built for cybersecurity use cases: continuous asset monitoring, vulnerability prioritization, vendor risk management, and compliance reporting mapped to frameworks like NIST CSF, HIPAA, DORA, GLBA, and SOC 2. FortifyData is a cyber GRC platform designed specifically for security and compliance teams rather than risk officers or auditors.
FortifyData’s platform includes attack surface management for continuous external and internal asset monitoring, third-party risk management with AI-powered vendor document auditing and auto-validated questionnaires, compliance automation that maps risk findings to framework controls automatically, vulnerability management with risk-based prioritization, security ratings for both internal posture monitoring and vendor benchmarking, and enterprise risk management for centralized risk oversight. All modules run on a unified data model which means findings from one module feed directly into the others.
FortifyData is built for CISOs, security directors, information security analysts, and vendor risk managers at mid-market organizations. It is particularly well-suited for security teams that are under-resourced relative to their responsibilities — organizations that need to manage a complex risk program without the headcount or budget of a large enterprise. FortifyData serves organizations across financial services, healthcare, higher education, energy and utilities, manufacturing, and technology sectors.
Traditional GRC platforms were built for broad enterprise risk management and typically require months to implement, significant configuration, and dedicated GRC administrators to maintain. FortifyData is purpose-built for cybersecurity use cases — it connects directly to live technical data from asset assessments rather than relying on manually entered risk information. Risk findings from attack surface scans, vendor assessments, and vulnerability management feed automatically into compliance reporting, eliminating the manual evidence collection that makes traditional GRC platforms resource-intensive. FortifyData is also significantly faster to deploy and more affordable than enterprise GRC platforms.
FortifyData supports compliance reporting and gap analysis across multiple frameworks including NIST CSF, NIST SP 800-53, ISO 27001, SOC 2, HIPAA, GLBA Safeguards Rule, DORA, PCI DSS, HITRUST, and HECVAT for higher education institutions. Risk findings from continuous asset assessments and vendor evaluations are automatically mapped to applicable framework controls, reducing the manual work of evidence collection and control mapping that consumes significant analyst time in traditional compliance programs.



